The Challenge
In February 2015, the space domain was designated as UK Critical National Infrastructure (CNI) by the Centre for the Protection of National Infrastructure (CPNI). Space satellites not only connect us to the internet and allow us to watch TV, but also underpin our national security and defence efforts. However, a better understanding of the technology required to defend future space assets is still being defined.
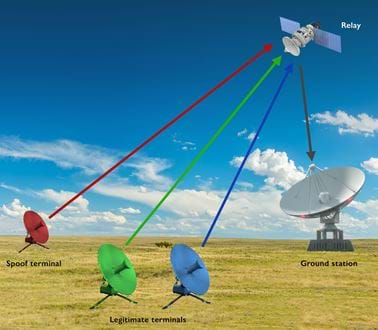
To address this, the Dstl Space Programme, in collaboration with the Defence & Security Accelerator (DASA), launched ‘Space to Innovate’, identifying four themes of significant interest to defence. Roke was one of three successful bidders under theme one: ‘Technologies for defending future UK space assets’. The focus is on using innovative technology to ensure the UK’s global communications operations are resilient to current and emerging threats, including jamming and cyber-attack. Our “defence against spoofing” concept uses Machine Learning (ML) techniques to discriminate legitimate users of SATCOM services from those attempting to spoof the system by falsifying data, in order to gain an illegitimate advantage.
The Approach
Building on previous research in other domains, but not previously applied to SATCOM, we directly addressed the emerging spoofing threat identified in recent assessments of SATCOM security. Our engineers collected signals from typical L-band SATCOM sources and applied ML based processing to demonstrate discrimination, at both the make/model and serial number level of the transmitter. Importantly, this included not only multiclass classification, where a signal is associated with one of any previously encountered sources in the training library; but also anomaly detection, where the signal can be flagged as not matching any known source. This allows timely action to be taken to limit interactions until the signal origin can be verified. Processing of signals collected for a range of equipment configurations shows that the classification is robust to variations in signal-to-noise ratio, power level, bandwidth and frequency, where these are captured in the training data.

THE OUTCOME
Our research offers the potential to discriminate individual SATCOM emitters/spoofers in the same geographic area, based on the unique “fingerprint” of the transmitter – independently of any claimed identity in the signal data. This is applicable to existing and future SATCOM receivers as additional software based signal processing, either at a ground terminal (downlink) or at the satellite itself (uplink). It enhances communications security and resource availability for legitimate users, and supports valuable intelligence gathering on spoofers.
Future work would seek to demonstrate the robustness of the approach for a wider range of signal types and equipment configuration, and to mature the concept to higher TRL, in collaboration with government, military users, and industrial partners.
Related news, insights and innovations
Find out more about our cutting-edge expertise.